No title
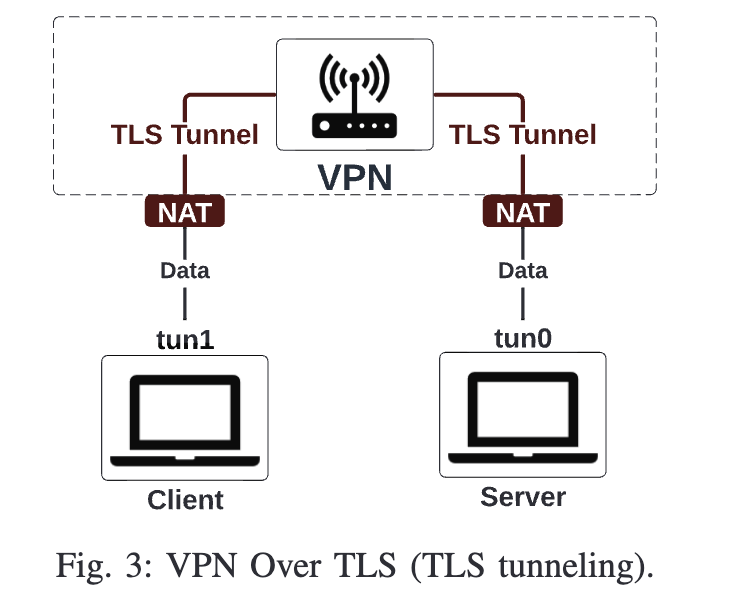
In this paper, they focused on integrating PQ-TLS protocols into 5G control plane. They proposed a VPN over TLS communication scheme, which can be used for NF registration messages and UE registration and authentication messages. In their VPN over TLS, they created tunneling between two communication entities, where all traffics were protected using TLS, and NAT was used for data transmission between two TUN interfaces.
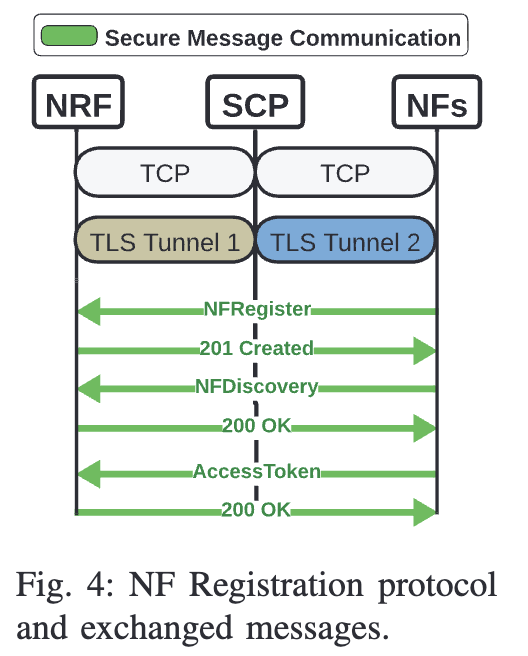
In the 5G scenario, they considered the Service Communication Proxy (SCP), which is responsible for managing and optimizing the communication between network functions within the 5G Core. Their research was based on that, in most cases, no TLS is deployed for control plane protection.
So they used their own VPN with PQ-TLS, to setup tunnels in NF registration. The SCP functions as the server for communications with other NFs.
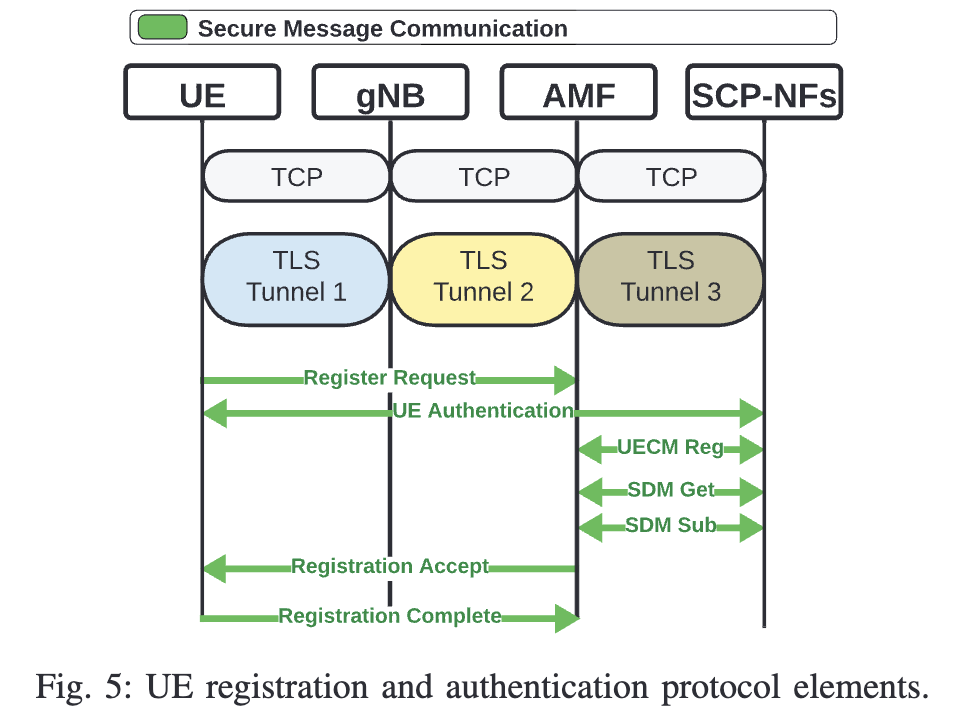
Additionally, they also applied the VPN into the UE registration. The gNB acts as the server, waiting for the UE’s TLS connection initiation; the AMF serves as the server for interactions with the gNB.
For real cases, they recommended users to use the built-in VPN framework, such as VpnService API in Android, Network Extension in IOS, OpenVPN or strongSwan in Linux. For testing, they created a python based VPN script and 5G-PQ-TLS-Tunnel integrating libOQS post-quantum library. They deployed Open5GS and UESIMRAN on the cloud and also real servers.
https://github.com/adwise-fiu/5G-PQ-TLS-Tunnel
https://github.com/dmitriykuptsov/vpn_over_tls
Introduction
Describes the advantages of 5G technology, including faster speeds, reduced latency, and enhanced coverage.
Highlights the need for enhanced security features in 5G networks, particularly for time-sensitive applications.
Presents Transport Layer Security (TLS) as a more secure alternative for 5G, emphasizing its robustness against classic attacks but vulnerability to quantum computer attacks.
Introduces Post-Quantum Cryptography (PQC) as a solution to address these quantum computing threats and mentions the Open Quantum Safe (OQS) project.
Proposes integrating PQ-TLS into 5G using existing open-source implementations without requiring major changes.
Describes the use of tunneling-based TLS for secure end-to-end Control Plane (CP) communications.
Related Work
Presents a review of existing research on TLS integration in 5G.
Mentions attempts to integrate TLS into 5G communications, highlighting their limitations to core network implementations and lack of post-quantum support.
Discusses efforts to integrate PQ-TLS for other communication technologies, like BLE and WiFi-based IoT.
Notes concerns and security weaknesses related to the use of EAP-TLS in 5G.
Background
Explains the process of TLS handshake and its importance in establishing trust between client and server.
Describes EAP-TLS as a mutual authentication method and its application in 5G networks.
Discusses post-quantum algorithms and their resistance to attacks from quantum computers, with a specific focus on Dilithium, Falcon, and SPHINCS signature scheme families.
Provides background on 5G architecture, including Control User Plane Separation (CUPS) and key Network Functions (NFs), such as AMF, UPF, NRF, AUSF, and SCP.
Proposed Approach
Explains the motivation for integrating TLS into the 5G Core Network and the limitations of open-source 5G implementations in terms of TLS support.
Discusses the advantages of VPN Over TLS for securing end-to-end communications and its benefits compared to EAP-TLS.
Describes the integration of TLS into NF registration, where NFs register with the NRF, using VPN over TLS for secure communication.
Explains the process of TLS integration into UE registration, which involves secure communication between UE, gNB, AMF, and other NFs using segmented TLS tunnels.
Performance Evaluation
Describes the experimental setup, including the use of Open5GS for 5G Network Core, UERANSIM for UE and gNB, and OQS-OpenSSL for PQ-TLS implementation.
Explains the use of two testbeds, Local Testbed and Cloud Testbed, hosted on physical devices and Google Cloud Platform (GCP), respectively.
Lists the metrics used for performance evaluation, including latency, packet size, number of messages, and energy consumption.
Presents the results of the experiments, comparing the performance of different TLS implementations with traditional and PQ certificates.
Conclusion
Summarizes the design and implementation of end-to-end TLS integrated into 5G communications using a tunneling approach.
Discusses the performance evaluation results, indicating that PQ-TLS approaches introduce a slight communication overhead, with some matching the performance of classical TLS approaches.
Highlights PQ-TLS using Falcon512 as the most efficient implementation.
Notes that TLS tunneling matched the performance of a regular EAP-TLS implementation.

